A new quantum cryptography protocol that is much faster has been developed: Typically, quantum cryptography is performed with photons that can exist in two states. Cryptographic keys can be generated much faster and with much greater robustness against interference when eight different states are used.
One of the most promising quantum technologies of our time is quantum cryptography: The exact same information is generated in two different locations, and quantum physics laws ensure that no third party can intercept this information. This generates a code that can perfectly encrypt information.
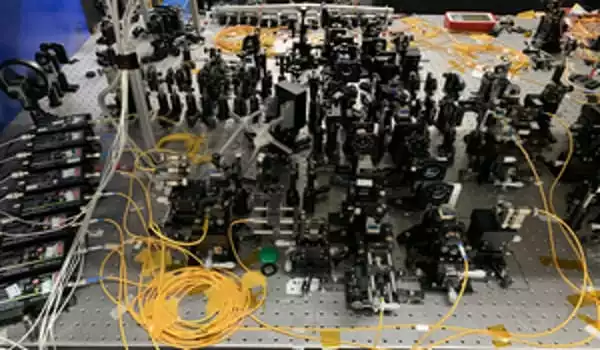
Prof. Marcus Huber’s team at the TU Wien Atomic Institute developed a new type of quantum cryptography protocol, which has now been tested in practice in collaboration with Chinese research groups: Previously, photons that could be in two different states were used; however, the situation here is more complicated: Each photon can take one of eight different paths. As the team has now demonstrated, this speeds up the generation of the quantum cryptographic key and makes it significantly more resistant to interference. The findings have now been published in the peer-reviewed journal Physical Review Letters.
A new and much faster quantum cryptography protocol has been developed. Using eight different states, cryptographic keys can be generated much faster and with much more robustness against interference.
Two states, two dimensions
“There are numerous ways to transmit information using photons,” says Marcus Huber. “Experiments frequently focus on the polarisation of their photons. For example, whether they oscillate horizontally or vertically, or whether they are in a quantum-mechanical superposition state in which they can be in both states at the same time. The state of the photon can be represented as a point in a two-dimensional space in the same way that a point on a two-dimensional plane can be described with two coordinates.”
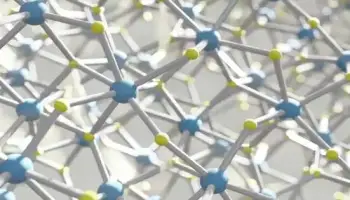
A photon, on the other hand, can carry information regardless of the direction of polarization. For example, the information about which path the photon is currently traveling on can be useful. This is precisely what is now being exploited: “In a special type of crystal, a laser beam generates photon pairs. This can happen at eight different points in the crystal “Marcus Huber explains. Depending on where the photon pair was created, each of the two photons can move along eight different paths or along several paths at the same time, which is also permitted by quantum theory’s laws.
These two photons can be directed to different locations and analyzed there. One of the eight possibilities is measured at random, but because the two photons are quantum-physically entangled, the same result is obtained in both locations. Whoever is standing at the first measuring device is aware of what another person is currently detecting at the second measuring device and no one else in the universe has access to this information.
Eight states, eight dimensions
“The fact that we use eight possible paths here, rather than two different polarisation directions, makes a big difference,” says Marcus Huber. “The space of possible quantum states expands significantly. The photon can no longer be described by a two-dimensional point; it now exists in eight dimensions.”
This has a number of advantages: For starters, it allows for the generation of more data: A new record in entanglement-based quantum cryptography key generation has been set at 8307 bits per second and more than 2.5 bits per photon pair. Second, it can be demonstrated that this reduces the process’s susceptibility to interference.
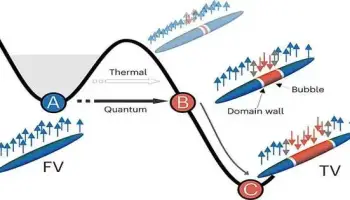
“You have to deal with the problem of decoherence with all quantum technologies,” says Marcus Huber. “No quantum system can be completely free of disturbances. However, if it comes into contact with a disturbance, it quickly loses its quantum properties: the quantum entanglements are destroyed.” Higher-dimensional quantum states, on the other hand, are less likely to lose their entanglement even when disturbed.
Furthermore, advanced quantum error-correction mechanisms can be used to compensate for the effects of external perturbations. “In the experiments, additional light was turned on in the laboratory to intentionally cause disturbances – and the protocol still worked,” Marcus Huber says. “But only if we took eight different routes. We were able to demonstrate that a cryptographic key can no longer be generated in this case using only a two-dimensional encoding.”
In theory, it should be possible to improve the new, faster, and more reliable quantum cryptography protocol even further by employing additional degrees of freedom or a greater variety of different paths. “However, this not only expands the space of possible states, but it also becomes increasingly difficult to read out the states correctly at some point,” says Marcus Huber. “We appear to have found a good compromise here, at least within the boundaries of what is currently technically possible.”